In January 2026 alone, cryptocurrency scams and exploits drained $370.3 million from victims (the highest monthly total in nearly a year). A single social engineering attack stole $284 million from one individual. Phishing schemes accounted for $311 million. And behind these numbers are real people: retirees, young investors, and even experienced crypto users who thought it “could never happen to them.”
The days of obvious “Nigerian prince” emails are long gone. In 2026, scammers use AI‑generated deepfake videos of Elon Musk promising to double your Bitcoin, fake trading platforms that look identical to real exchanges, and months‑long “pig butchering” romance schemes that drain life savings. The most dangerous attacks no longer exploit code, they exploit human psychology.
This guide is your complete defense manual. We’ll walk through every major scam type active in 2026, show how to avoid crypto scams, exactly how to spot red flags, give you step‑by‑step protection protocols, and, if the worst happens, tell you exactly what to do to maximize your chances of recovery. Your crypto is valuable. Let’s make sure you keep it.

Why Scams Are Surging in 2026: The New Threat Landscape
The Numbers Are Staggering
According to blockchain security firm CertiK, crypto losses reached $370.3 million in January 2026, a nearly fourfold increase from January 2025. Chainalysis reports that illicit cryptocurrency addresses received a record $154 billion in 2025, and 2026 is on track to match or exceed that figure.
The Shift from Code Exploits to Human Exploits
In previous years, the biggest threats were smart contract bugs and exchange hacks. That’s changed. Phishing and social engineering now cause the majority of losses ($311 million in January alone), or 84% of total theft. Attackers are targeting the weakest link in any security system: human psychology.
Why 2026 Is Different
| Factor | Impact |
|---|---|
| AI Deepfakes | Real‑time video and audio of celebrities promoting fake giveaways |
| Wallet Drainers as a Service | Automated toolkits that drain wallets via fake approvals |
| Industrialized Pig Butchering | Organized crime rings running “fraud factories” with human trafficking victims |
| Cross‑Chain Complexity | Multiple chains make tracking stolen funds harder |
| Regulatory Gaps | Scammers operate across borders where enforcement is weak |
The One Scam That Skews the Numbers
In January 2026, a single victim lost approximately $284 million in a large‑scale social engineering attack (nearly 75% of the month’s total losses). While this is an extreme outlier, it proves a terrifying point: one mistake can cost everything.
The 10 Most Common Crypto Scams in 2026

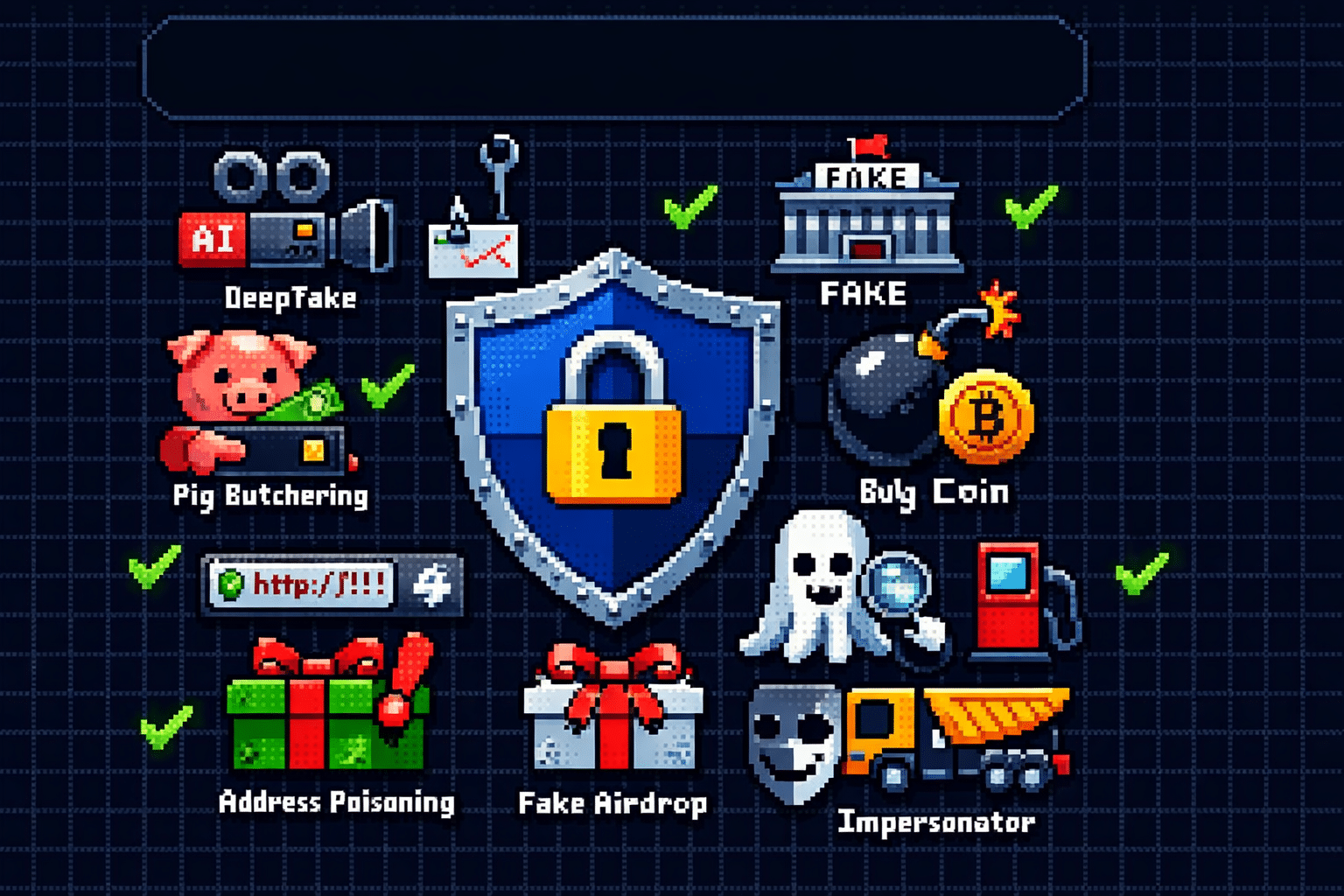
1. AI Deepfake Scams
What It Is: Scammers use artificial intelligence to create realistic videos and audio of public figures, Elon Musk, Vitalik Buterin, Donald Trump, promising to “double your crypto” if you send it to a wallet address first.
How It Works
- Scammers create a deepfake video using AI.
- The video appears on YouTube, X, or Telegram showing a “live” stream.
- A fake “giveaway” promises to double any crypto sent.
- Victims send funds expecting double back, and lose everything.
2026 Case: A deepfake Musk YouTube stream collected over $5 million in 20 minutes. The funds were quickly laundered through mixers and darknet markets.
Red Flags
- “Send 1 BTC, get 2 back” promises
- Unverified social media accounts
- Countdown timers creating urgency
- Links in video descriptions (not official channels)
Protection: Never send crypto to anyone promising to double it. Legitimate giveaways never require sending funds first. Always verify announcements from official project websites, not social media.
2. Phishing and Wallet Drainers
What It Is: Phishing attacks use fake emails, websites, or messages that mimic legitimate platforms to steal your private keys or seed phrase. Wallet drainers are automated scripts that sweep funds once you approve a malicious transaction.
How It Works
- You receive an email claiming “your wallet needs verification” or “urgent security update.”
- The link leads to a fake website that looks identical to MetaMask, Coinbase, or your exchange.
- You enter your seed phrase or approve a transaction.
- The drainer script immediately transfers all assets to the scammer’s wallet.
2026 Case: A California victim lost $100,000 after clicking a Discord “support” link to a fake Arkadiko site. Another victim’s hardware wallet was drained via a fake airdrop that tricked them into approving a malicious contract. $7,800 gone.
Red Flags
- Urgent “verify your wallet” requests
- URLs with typos (
binanace.comvsbinance.com) - Emails claiming your account is locked
- Requests for your seed phrase (legitimate services never ask)
Protection
- Bookmark official exchange and wallet URLs
- Never click links in emails or DMs
- Use hardware wallets for large holdings
- Enable 2FA (preferably hardware keys like YubiKey)
- Revoke unused token approvals at Revoke.cash
3. Pig Butchering (Romance Scams)
What It Is: A long‑term con where scammers build trust through romantic or friendly relationships over weeks or months, then introduce a “high‑return” crypto investment platform they control.
Why It’s Called “Pig Butchering”: The scammer “fattens the pig” by building emotional connection and showing fake profits, then “butchers” by stealing everything when the victim tries to withdraw.
How It Works
- Scammer contacts you via dating app, social media, or “wrong number” text.
- They build a relationship over weeks – sharing photos, life stories, future plans.
- They claim to have a secret crypto trading strategy with guaranteed returns.
- They show a fake dashboard where your initial small investment “grows.”
- When you try to withdraw, they demand fees, taxes, or more investment.
- The platform vanishes, and so does the scammer.
2026 Case: A Maryland woman lost millions to Southeast Asian pig butchering scammers. When she tried to get help, “recovery” firms stole even more. The UN estimates over 200,000 people are trafficked to operate these scam centers.
Red Flags
- Unsolicited messages on dating apps or WhatsApp
- Someone who quickly professes love or deep friendship
- Vague explanations of their “crypto expertise”
- Pressure to invest without doing your own research
- Refusal to video call (scammers hide their identity)
Protection
- Never share your wallet screens or portfolio
- Ask for LinkedIn, Facebook, or other verifiable accounts
- If someone you’ve never met asks for crypto, it’s a scam
- Report to FBI IC3 and local authorities
4. Fake Investment Platforms
What It Is: Websites and apps that look like legitimate exchanges but are designed to steal deposits. Users see fake profits on a dashboard, but withdrawals are blocked with endless “taxes” and “fees.”
How It Works
- You’re invited to a platform via social media or a “friend.”
- The site looks professional (charts, testimonials, security badges).
- Your first small deposit “earns” high returns.
- You deposit more.
- When you try to withdraw, you’re told to pay “taxes” or “network fees.”
- The platform disappears.
2026 Case: An Australian victim lost $64,000 to Ultra Trade via Signal. The platform showed fake profits, but every withdrawal attempt required more fees. A Cyprus victim lost $37,000 in a similar scheme.
Red Flags
- Promises of guaranteed returns (10‑50% monthly)
- No regulatory licenses visible
- Anonymous team
- Pressure to deposit more to unlock funds
Protection
- Only use exchanges from our Best Crypto Exchanges list
- Verify licenses with local regulators
- Search “[platform name] scam” before depositing
5. Rug Pulls and Honeypot Tokens
What It Is: Rug pulls occur when developers create a token, hype it up, then drain all liquidity, leaving the token worthless. Honeypot tokens are coded so you can buy but never sell.
How It Works
- Scammers create a new token with hype marketing.
- They lock liquidity briefly, making it look safe.
- Early investors see price rise.
- Developers dump their holdings or remove liquidity.
- Price crashes to zero; investors can’t sell.
2026 Case: Meteora (Solana) insiders controlled 95% of supply through 150 wallets, pumped the price, and dumped. Retail investors lost $69 million. Kokomo Finance stole $5.5 million via malicious code.
Red Flags
- Top 10 wallets hold >50‑80% of supply
- Liquidity locked for less than 6 months
- Anonymous team with no verifiable history
- No security audit from reputable firms
Protection:
- Check token distribution on Etherscan or Solscan
- Use Honeypot.is or TokenSniffer to scan contract addresses
- Look for audits from CertiK, Hacken, Trail of Bits
- Never invest in tokens you don’t understand
6. Address Poisoning
What It Is: Scammers send a tiny $0 transaction from a wallet address that looks almost identical to one you’ve used before. If you copy from your transaction history instead of your saved address, you send funds to the scammer.
How It Works
- Scammer tracks your frequent transaction addresses.
- They generate a “vanity address” matching the first and last characters of your real address.
- They send a $0 transaction from that fake address.
- Your transaction history now shows both addresses.
- You accidentally copy the fake address from history.
- Your funds go to the scammer.
2026 Case: In February 2026, a victim sent approximately $600,000 to a poisoning address. The intended address was 0x77f6ca8E...a346; the poison address was 0x77f6A6F6...A346.
Red Flags
- Unexpected $0 transactions in your wallet
- Addresses with similar first/last characters to yours
Protection
- Always verify the full address, not just first/last characters
- Use saved address books (whitelists) on exchanges
- Test with small amounts before large transfers
- Use hardware wallets that display full addresses on screen
7. Fake Airdrops and Giveaways
What It Is: Scammers promote fake token airdrops requiring you to “connect wallet to claim.” When you connect and approve, a drainer script empties your wallet.
How It Works
- Scammers create a website for a “new token airdrop.”
- They promote it on Telegram, X, or Discord.
- You connect your wallet to claim.
- The site requests approval to spend your tokens.
- All assets are drained instantly.
2026 Case: A fake Uniswap v4 airdrop stole over $500 million from victims who connected their wallets to claim nonexistent tokens. In February 2026, a fake Uniswap phishing site caused over 1,000 victims to lose approximately $1.8 million.
Red Flags
- “Claim your free tokens” links
- Unsolicited airdrop announcements
- Deadlines creating urgency
- Requests to approve contracts
Protection
- Only interact with official project websites (bookmarked, not searched)
- Never approve contracts for “free” tokens
- Use a separate wallet for airdrops
- Revoke approvals after use at Revoke.cash
8. Recovery Scams
What It Is: After you’ve already been scammed, fraudsters contact you claiming they can recover your funds, for an upfront fee. They take your money and disappear.
How It Works
- Scammers monitor scam victim reports.
- They contact you offering “blockchain forensic services” or “legal recovery.”
- They demand upfront payment for investigation.
- After payment, they vanish or demand more fees.
2026 Case: Pig butchering victims paid over $100,000 to fake lawyers promising fund recovery. The scammers just stole more.
Red Flags
- Guarantees of recovery (no one can guarantee this)
- Requests for upfront payment
- Unsolicited outreach claiming they’ve “found your funds”
Protection:
- No legitimate recovery service demands payment before work
- File official reports with law enforcement first
- The FBI IC3 and state Attorney General offices offer free assistance
9. Impersonation and Tech Support Scams
What It Is: Scammers pose as government officials, exchange support, or hardware wallet representatives, claiming your funds are at risk and requiring “verification”, which means handing over your seed phrase or sending crypto.
How It Works
- You receive a call, text, or email claiming to be from Coinbase, Ledger, or the IRS.
- They claim suspicious activity on your account.
- They demand you “verify” your wallet or send funds to a “safe” address.
- If you comply, funds are stolen.
2026 Case: A 23‑year‑old Brooklyn resident was charged with stealing $16 million from Coinbase users by posing as a Coinbase employee and pressuring victims to transfer crypto to wallets he controlled.
Red Flags
- Unexpected calls claiming your funds are at risk
- Requests for seed phrase or private keys
- Pressure to act immediately
Protection
- The IRS, exchanges, and wallet providers never ask for seed phrases
- Hang up and call the official number yourself
- Enable anti‑phishing codes on exchanges
10. Pump-and-Dump Schemes
What It Is: Groups coordinate on Telegram or Discord to hype low‑cap tokens, pumping the price, then selling (dumping) on retail investors who buy the hype.
How It Works
- A group acquires a large position in a low‑cap token.
- They promote it on social media with “1000x” promises.
- Retail investors FOMO in, driving price up.
- The group sells into the pump, leaving retail holding worthless tokens.
Red Flags
- “To the moon” shilling
- Telegram channels promising guaranteed gains
- Tokens with less than $1 million market cap
- No clear utility or development activity
Protection
- Avoid low‑cap tokens promoted by anonymous groups
- Check holder distribution on DEX tools
- If you didn’t research it, don’t buy it
How to Research Any Crypto Project Before Investing
The 5‑Step Research Framework
Step 1: The Team Audit
Start with the humans. While anonymous founders are part of crypto culture, they represent massive risk.
| Check | What to Look For |
|---|---|
| Public team members | Real names, LinkedIn profiles, work history |
| Mutual connections | Do they know other industry professionals? |
| Reverse image search | Are their photos stolen from stock image sites? |
| Previous projects | Have they built successful projects before? |
Step 2: The Tokenomics Analysis
Next, look at the supply distribution. A project where the top 10 wallets hold 80% of supply is a disaster waiting to happen.
| Metric | What to Check |
|---|---|
| Holder distribution | Top 10 wallets should hold <50% |
| Vesting schedule | Team and investor unlocks should be gradual, not all at once |
| Liquidity lock | Locked for at least 6‑12 months |
| Total supply | Is there a cap? Inflation rate? |
Step 3: The Smart Contract Check
You don’t need to be a coder to check basic security. Use free tools and audits.
| Check | How To |
|---|---|
| Security audit | Look for audits from CertiK, Hacken, Trail of Bits – and read the PDF! |
| Honeypot check | Use Honeypot.is or TokenSniffer to scan contract addresses |
| Contract verification | On Etherscan, look for the verified checkmark |
| Admin keys | Are there renounced ownership or timelocks? |
Step 4: The Community Vibe Check
Join their Discord or Telegram. Watch the conversation. A healthy community discusses technology, not just price.
| Green Flags | Red Flags |
|---|---|
| Technical questions about roadmap | “When moon?” and “Buy the dip” spam |
| Constructive criticism | Banning legitimate questions |
| Active development discussions | Price speculation only |
| Team engagement | Anonymous team, no responses |
Step 5: External Validation
Finally, search the internet, but with the right keywords.
- Search
[project name] scamor[project name] reddit - Check Twitter for independent analysis (not shills)
- Verify project is listed on CoinGecko or CoinMarketCap with legitimate volume
How to Choose a Secure Exchange and Wallet
For Centralized Exchanges: The 3‑Pillar Security Framework
1. Proof of Reserves (PoR)
Never trust an exchange that says “trust me.” Look for monthly cryptographic proof that shows the exchange actually holds the assets they claim to owe customers.
| What to Check | Why It Matters |
|---|---|
| Monthly PoR reports | Regular verification, not one‑time |
| Third‑party auditor | Independent verification, not self‑reported |
| Merkle tree proofs | Cryptographic proof, not just a PDF |
2. Regulatory Compliance
Operate in the light. Regulated exchanges are subject to audits and legal standards that protect you.
| What to Check | Why It Matters |
|---|---|
| Licenses | US, Canada, EU, UK licenses |
| Public company status | SEC reporting requirements |
| Insurance funds | Binance SAFU ($1B+), Bitget Protection Fund ($300M+) |
3. Security History
Google the exchange name + “hack.” Has the platform ever lost user funds? If yes, did they reimburse victims?
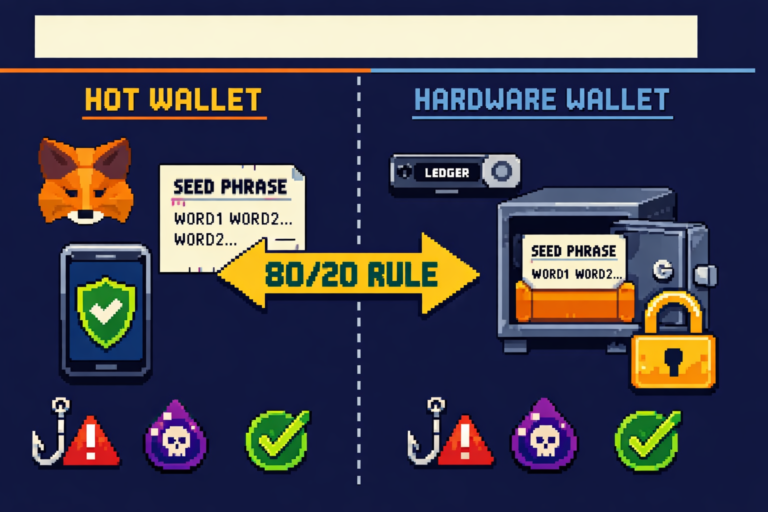
For Wallets
| Wallet Type | Best For | Security Practice |
|---|---|---|
| Hardware wallet (Ledger/Trezor) | Long‑term holdings >$1,000 | Keys never touch internet |
| Software wallet (MetaMask, Phantom) | Daily use, small amounts | Always verify addresses, revoke approvals |
| Exchange wallet | Trading only | Never leave large amounts |
Essential Security Tools and Habits
The 10 Commandments of Crypto Security
- Never share your seed phrase. Not with support, not with “verification,” not with anyone. Period.
- Bookmark official sites. Don’t search for exchanges, you’ll find ads for fake sites. Uniswap’s fake phishing site stole $1.8M in February 2026 alone.
- Verify full addresses. Check at least 4‑6 characters on both ends, not just first/last.
- Test with small amounts. Before moving large sums, send $5‑10. Confirm arrival, then send the rest.
- Use hardware wallets for savings. Hot wallets are for spending; cold storage is for wealth.
- Revoke approvals monthly. Unused smart contract approvals are open doors. Use Revoke.cash.
- Enable 2FA everywhere. Use authenticator apps, not SMS. SMS can be SIM‑swapped.
- Never click links in DMs. Every crypto Twitter thread has bots posting phishing links. Bookmark instead.
- Don’t trust, verify. Anyone promising guaranteed returns is lying. Risk and reward are inseparable.
- Slow down. Scammers use urgency to bypass your judgment. If it’s urgent, it’s a scam.
The “Too Good to Be True” Rule
If a website promises 10% daily returns, a celebrity is “doubling your crypto,” or a stranger wants to teach you their “secret trading strategy”, STOP. It’s a scam. Real investments don’t work this way. The moment you feel FOMO (Fear Of Missing Out), that’s the signal to walk away.
What to Do If You’ve Been Scammed
Immediate Actions (Within Minutes)
1. Stop All Further Payments
Do not send more money. Scammers will claim “taxes,” “network fees,” or “unlocking fees” are needed. They’re not. Any further payment is lost.
2. Secure Remaining Funds
- If your wallet was compromised, move remaining funds to a new wallet immediately.
- Change exchange passwords.
- Revoke all token approvals.
- Enable withdrawal whitelisting.
3. Preserve All Evidence
| Evidence Type | What to Collect |
|---|---|
| Wallet addresses | Sender and receiver addresses |
| Transaction hash IDs | The unique identifier for each transaction |
| Dates and times | When each transaction occurred |
| Communications | Screenshots of chats, emails, texts |
| Platform screenshots | Dashboards showing fake profits, error messages |
Step 2: Report the Scam
Where to Report
| Jurisdiction | Where to File |
|---|---|
| United States | FBI IC3 (ic3.gov); local police; state Attorney General |
| Massachusetts (example) | Massachusetts AGO has deactivated 50+ scam websites and returned $6M to victims |
| India | cybercrime.gov.in |
| International | Local law enforcement; exchange compliance teams |
What to Include in Your Report
- All transaction hash IDs
- Wallet addresses involved
- Communications with scammers
- Timeline of events
Step 3: Can You Recover Stolen Funds?
The short answer: maybe. While blockchain transactions are irreversible, they are also transparent. Every transaction leaves a permanent, traceable record.
Factors That Increase Recovery Chances
| Positive Factor | Why It Helps |
|---|---|
| Funds passed through a centralized exchange | Regulated exchanges can freeze accounts |
| You reported quickly | Faster action = less time for funds to move |
| You have transaction hash IDs | Essential for tracing |
| Law enforcement involved | Official reports increase cooperation |
How Recovery Works
- Blockchain tracing: Investigators map the path of stolen funds across wallets.
- Identify exchange touchpoints: When funds hit a regulated exchange, accounts can be frozen.
- Legal action: Law enforcement or lawyers compel exchange cooperation.
- Potential seizure: If funds are identified and frozen, they may be returned.
Important Warnings
- No one can guarantee recovery. Anyone promising guaranteed recovery is scamming you again.
- Recovery takes time. It’s measured in months, not days.
- Costs may be involved. Legal and forensic services may charge fees, but never upfront.
What Recovery Services Like Forensic Logic Inc Do
Professional blockchain forensic firms use structured analytics to reconstruct the movement of stolen assets, map transactions across multiple networks, and identify exchange deposit points. This documentation can be used for regulatory or law enforcement escalation.
Crypto Scam Red Flags: The Ultimate Checklist
Print this list. Share it. Live by it.
Investment Red Flags
| Red Flag | Why It’s Dangerous |
|---|---|
| “Guaranteed returns” | No legitimate investment guarantees returns |
| “Double your crypto” | Always a scam |
| Secret trading algorithm | Scammers create fake dashboards |
| Pressure to act now | Urgency bypasses judgment |
| Exclusive group invite | Preys on FOMO |
Project Red Flags
| Red Flag | Why It’s Dangerous |
|---|---|
| Anonymous team | No accountability; rug pull risk |
| No security audit | Code could be malicious or buggy |
| Top 10 wallets hold >50% supply | One entity can dump price |
| Liquidity locked <6 months | Devs can pull liquidity anytime |
| Whitepaper is plagiarized | No real project behind the hype |
Platform Red Flags
| Red Flag | Why It’s Dangerous |
|---|---|
| No Proof of Reserves | Exchange may not have your funds |
| No regulatory licenses | No oversight, no recourse |
| History of hacks without compensation | Your funds may not be safe |
| No 2FA options | Easier to hack |
Communication Red Flags
| Red Flag | Why It’s Dangerous |
|---|---|
| “Your wallet needs verification” | Scam to get seed phrase |
| “Send crypto to this address” | Legitimate services never ask this |
| Urgent security alert | Scammers create panic |
| Unsolicited DMs | Especially on Discord/Telegram |
| “I can help recover your funds” | Recovery scam |
The Golden Rule
If something feels off, it probably is. Trust your gut. No legitimate opportunity requires you to act immediately, send crypto to verify, or share your seed phrase. When in doubt, step back, research, and ask in trusted communities before sending anything.
Next Steps: From Awareness to Action
You now know how to spot scams. Here’s how to protect yourself starting today.
The 15-Minute Security Audit
| Task | Time | Action |
|---|---|---|
| Revoke approvals | 5 min | Visit Revoke.cash, revoke unused approvals |
| Enable 2FA | 5 min | Switch from SMS to authenticator app; enable withdrawal whitelist |
| Backup seed phrase | 5 min | Ensure seed is on paper (not digital) in a secure location |
The Weekly Security Habit
- Check your wallet for unexpected transactions
- Review new approvals
- Stay informed about new scam techniques
Essential Next Reads
- 📚 Best Crypto Exchanges 2026: Secure Platforms
- 📚 What is a Hardware Wallet? Complete Guide
- 📚 How to Set Up a Secure Crypto Wallet
- 📚 Crypto Security: Advanced Protection
Join the Community
Security is a community effort. Share this guide with friends new to crypto. Join our Discord for scam alerts and security discussions. Follow us on Twitter for real‑time warnings about new threats.
Final Thought
The crypto space offers incredible opportunity, but it’s also a minefield for the unprepared. Scammers are sophisticated, patient, and ruthless. But they only win when we let our guard down.
By following the principles in this guide (verify everything, secure your keys, trust your gut) you can navigate this space safely. Your crypto is valuable. Protect it like it is.
Disclaimer: This guide is for educational purposes only and does not constitute legal or financial advice. If you believe you have been scammed, contact local law enforcement and file a report with the relevant authorities. No recovery service can guarantee the return of stolen funds.
This guide was last updated for the 2026 edition. Scam tactics evolve daily – stay informed through trusted security communities and official channels.
Frequently Asked Questions
What are the most common crypto scams in 2026?
The top threats are: AI deepfake videos promising to double crypto, phishing and wallet drainers, pig butchering romance scams, fake investment platforms, rug pulls, address poisoning, fake airdrops, recovery scams, impersonation scams, and pump‑and‑dump schemes. Phishing alone caused $311 million in losses in January 2026.
Can I get my money back after a crypto scam?
Possibly, but it’s not guaranteed. If stolen funds pass through a regulated exchange, accounts can be frozen. Immediate reporting, preserving transaction hashes, and filing police reports increase your chances. No legitimate service guarantees recovery. Anyone claiming they can is likely scamming you again.
How do scammers get my seed phrase?
Scammers trick you into sharing it. Common tactics: fake “wallet verification” emails, fake support calls, malicious websites that look like MetaMask or Ledger Live, and phishing links in Discord DMs. Legitimate services never ask for your seed phrase.
What is pig butchering in crypto?
Pig butchering is a long‑term romance scam where criminals build trust over weeks or months, then introduce a fake crypto investment platform. Victims see fake profits on a dashboard but can never withdraw. The scam is named for “fattening the pig” (building trust) before “butchering” (stealing everything).
How to check if a token is a honeypot?
Use free tools like Honeypot.is or TokenSniffer. Scan the contract address before buying. Honeypots are coded so you can buy but never sell (the scammer controls the contract).
Are crypto giveaways real?
Legitimate giveaways never require sending crypto first. Any “send 1 BTC, get 2 back” promise is 100% a scam. Verified exchanges may run promotions, but they never ask you to send funds to an external wallet.
What should I do if I get scammed?
Immediately stop all payments, secure remaining funds, and preserve evidence (transaction hashes, wallet addresses, screenshots). Then file a report with FBI IC3 (US), local police, and your state Attorney General. For Massachusetts residents, the AGO has returned $6M to victims.
Is my crypto safe on an exchange?
Exchanges are convenient for trading but risky for long‑term storage. They can be hacked, freeze accounts, or go bankrupt (FTX). Use exchanges with Proof of Reserves and insurance funds, but move long‑term holdings to a hardware wallet.
How to spot a fake exchange?
Red flags: no Proof of Reserves, anonymous team, no regulatory licenses, promises of guaranteed returns, pressure to deposit quickly. Check our exchange reviews for vetted platforms. In February 2026, a fake Uniswap phishing site stole $1.8M from 1,000+ victims. Always bookmark official URLs.
What is address poisoning?
Scammers send a $0 transaction from an address that looks almost identical to one you’ve used before. If you copy from transaction history instead of your saved address, you send funds to the scammer. Always verify the full address, not just first and last characters.
How do I revoke token approvals?
Go to Revoke.cash, connect your wallet, and review all active approvals. Revoke any you don’t recognize or no longer use. This prevents drainers from accessing your funds.
Are hardware wallets worth it?
If you hold more than $1,000 in crypto, yes. Hardware wallets keep your private keys offline, making remote theft impossible. The $50‑150 cost is cheap insurance for your savings.
What are crypto recovery scams?
After you’ve been scammed, fraudsters contact you claiming they can recover your funds for an upfront fee. They take your money and disappear. No legitimate service guarantees recovery; always file official reports first.
How do I avoid phishing scams?
Bookmark official exchange and wallet URLs, never search for them. Don’t click links in emails or DMs. Enable anti‑phishing codes on exchanges. Use hardware wallets for verification. If you receive a “security alert,” contact the platform through official channels, not the message you received.